Wednesday, December 12, 2012
Google+ Communities
https://plus.google.com/communities/112334653322946592345
https://plus.google.com/communities/102507796610000516744
https://plus.google.com/communities/105032863651771032397
https://plus.google.com/communities/113808348632587763981
Don't be left out!
Thursday, December 06, 2012
Getting Netflix on the Big Screen, With Sound
This is an experiment in streaming Netflix to my TV, with audio going through the home theater speakers. Lots of devices can stream Netflix of course, but I happen to be fresh out of working solutions. So I'm going to use my phone.
The phone is a Samsung Galaxy SIII. An adapter is available for this phone that outputs an ordinary HDMI signal path, from the phone's USB jack.
Warning... Samsung used a non-standard pin layout on the port on the SIII. To do this, one must buy the Samsung HDMI device, specifically for the SIII. Others will not work. And the SIII device will not work with other Samsung phones. Apparently Samsung needed some extra funds for the executive Christmas party.
There are adapters for the SII from Samsung and other vendors, less expensive naturally.
First, there is a problem. I want the audio to go to my receiver, not to my TV. My TV has HDMI inputs, but my older receiver does not. I could use the TV speakers, but where's the fun in that? Enter this device.
This photo shows one end of a nifty little box that splits off the multi-channel audio from a digital HDMI signal to analog. On this end we see an HDMI input, a mode selection switch and the power input.
A word of warning. HDMI is a copy-protected format (for your protection). Not all boxes that claim to split the signal in this way will actually pass through the video (for your own good). This box worked for me, and my SIII, with Netflix. That's about all I can claim.
Here is the other end. The outputs are four stereo mini-jacks providing all the signals for 7.1 audio. There is also an optical output. And at the left end is the HDMI output for video to my TV.
Here's the cables I used. These have a mini-jack at one end, and RCA jacks on the other. Four of these get you to 8 channels, for 7.1 sound.
I'm going to connect the optical cable as well.
All set.
Next, here is the Samsung HDMI adapter. This connect to the phone at the small end, and provides a female HDMI port at the large end.
Note that this means I need another HDMI cable. I should have thought of that...
Also, this device will not work unless it is powered. It has a USB jack on it, just like the phone and is designed to be connected to the phone's charger.
A few things though...
The video signal from Netflix on the TV looked terrible, unwatchable in fact, for a couple minutes or more. Then apparently it realized it could use more bandwidth and stepped it up to something not too bad.
Also this setup might be a little flaky. It took awhile for the video signal to appear on the screen, although connecting the phone directly to the TV worked fine. The splitter box seems to have some trouble kicking in. It dropped out on me for a few seconds once too.
And of course Netflix is not pushing down multi-channel audio, but for old TV shows, that's OK.
All in all, so far so good. This looks like a usable setup for now.
The phone is a Samsung Galaxy SIII. An adapter is available for this phone that outputs an ordinary HDMI signal path, from the phone's USB jack.
Warning... Samsung used a non-standard pin layout on the port on the SIII. To do this, one must buy the Samsung HDMI device, specifically for the SIII. Others will not work. And the SIII device will not work with other Samsung phones. Apparently Samsung needed some extra funds for the executive Christmas party.
There are adapters for the SII from Samsung and other vendors, less expensive naturally.
First, there is a problem. I want the audio to go to my receiver, not to my TV. My TV has HDMI inputs, but my older receiver does not. I could use the TV speakers, but where's the fun in that? Enter this device.
This photo shows one end of a nifty little box that splits off the multi-channel audio from a digital HDMI signal to analog. On this end we see an HDMI input, a mode selection switch and the power input.
A word of warning. HDMI is a copy-protected format (for your protection). Not all boxes that claim to split the signal in this way will actually pass through the video (for your own good). This box worked for me, and my SIII, with Netflix. That's about all I can claim.
Here is the other end. The outputs are four stereo mini-jacks providing all the signals for 7.1 audio. There is also an optical output. And at the left end is the HDMI output for video to my TV.
Here's the cables I used. These have a mini-jack at one end, and RCA jacks on the other. Four of these get you to 8 channels, for 7.1 sound.
I'm going to connect the optical cable as well.
All set.
Next, here is the Samsung HDMI adapter. This connect to the phone at the small end, and provides a female HDMI port at the large end.
Note that this means I need another HDMI cable. I should have thought of that...
Also, this device will not work unless it is powered. It has a USB jack on it, just like the phone and is designed to be connected to the phone's charger.
It works!
A few things though...
The video signal from Netflix on the TV looked terrible, unwatchable in fact, for a couple minutes or more. Then apparently it realized it could use more bandwidth and stepped it up to something not too bad.
Also this setup might be a little flaky. It took awhile for the video signal to appear on the screen, although connecting the phone directly to the TV worked fine. The splitter box seems to have some trouble kicking in. It dropped out on me for a few seconds once too.
And of course Netflix is not pushing down multi-channel audio, but for old TV shows, that's OK.
All in all, so far so good. This looks like a usable setup for now.
Wednesday, August 08, 2012
HTTPS in jBoss 6
In setting up a jBoss 6 server for SSL, I found quite a bit of information was not readily available and there were several unexpected issues. Here's the long and short...
First, the server will need a keystore with a self-signed certificate. Use keytool, and an alias of "tomcat". I'll gloss over some of these general certificate steps because they are well covered in other places.
keytool -genkey -alias tomcat -keyalg RSA -keystore somekeyfile -validity 9999
In the first question, for first and last name, use the name that this server will be refereed to as, in client calls; "localhost", a hostname or an IP address. Use "changeit" for the passwords.
Next, extract the certificate just created from this file and set it aside.
keytool -export -keystore mykey -storepass changeit -alias tomcat -file tomcat.crt
I'm going to ultimately use this same store as both the key store and the trust store, so I re-import this certificate with the alias that the machine will be referred to. For example:
keytool -import -alias 192.168.0.8 -file tomcat.crt -keystore somekeyfile -storepass changeit
Now the file has the self-signed certificate, which the server will hand to clients making requests, and the same certificate, with the different alias, that clients will compare the server's certificate to, when making calls to this host.
Edit the follow file to enable the use of this keystore.
[server directory]/server/default/deploy/jbossweb.sar/server.xml
You can set the SSL port here too, like this.
<!-- SSL/TLS Connector configuration using the admin devl guide keystore --
port="8643" address="${jboss.bind.address}"
scheme="https" secure="true" clientAuth="false"
keystoreFile="${jboss.server.home.dir}/conf/somekeyfile"
keystorePass="changeit"
truststoreFile="${jboss.server.home.dir}/conf/somekeyfile"
truststorePass="changeit"
sslProtocol = "TLS" />
As an aside, I am using a port set that is supposed to add 200 to all my puts. This did not work for the SSL port, so I set it to the normal port + 200 as above, is server.xml.
Note that "truststore" properties are specified above, and some documentation indicates that this works. It does not. The keystore specification works however. The server will use the "tomacat" aliased certificate in the given file as it's own. I don't believe setting "truststoreFile" in server.xml has any impact.
For the truststore, clients will actually use the JRE's system trust store file. If nothing else is done but the above, to continue this example, then when this server attempts to access https://192.168.0.8:8643/something/ an exception will be thrown.
sun.security.validator.ValidatorException: PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target
This happens because the server certificate, the "tomcat" certificate provided by the server on the initial handshake, can't be found in the JRE truststore file. I added it to the somekeyfile above, but this file it not being checked. Options...
1. Add the certificate to the Jave truststore file, with the proper alias.
keytool -import -alias iws03qa5 -file tomcat.crt -keystore /opt/jdk1.6.0_30/jre/lib/security/cacerts -storepass changeit
2. Use properties set at the Java command line to specify a truststore location.
-Djavax.net.ssl.trustStore=[path and filename]
-Djavax.net.ssl.trustStorePassword=changeit
3. Set the truststore in jBoss's SSL support properties. To do this, edit:
[server directory]server/default/conf/bootstrap/security.xml
Add this, at the bottom, inside the "deployment" block:
[path]/server/default/conf/somekeyfile
changeit
[path]/server/default/conf/somekeyfile
changeit
Change [path] to your server path of course.
Interestingly, keystore properties must be given here also, even though they also appear in the other file. Otherwise, the security system will not initialize and it's a big mess.
With this setup, and the server bounced of course, the certificate is found and HTTPS works.
First, the server will need a keystore with a self-signed certificate. Use keytool, and an alias of "tomcat". I'll gloss over some of these general certificate steps because they are well covered in other places.
keytool -genkey -alias tomcat -keyalg RSA -keystore somekeyfile -validity 9999
In the first question, for first and last name, use the name that this server will be refereed to as, in client calls; "localhost", a hostname or an IP address. Use "changeit" for the passwords.
Next, extract the certificate just created from this file and set it aside.
keytool -export -keystore mykey -storepass changeit -alias tomcat -file tomcat.crt
I'm going to ultimately use this same store as both the key store and the trust store, so I re-import this certificate with the alias that the machine will be referred to. For example:
keytool -import -alias 192.168.0.8 -file tomcat.crt -keystore somekeyfile -storepass changeit
Now the file has the self-signed certificate, which the server will hand to clients making requests, and the same certificate, with the different alias, that clients will compare the server's certificate to, when making calls to this host.
Edit the follow file to enable the use of this keystore.
[server directory]/server/default/deploy/jbossweb.sar/server.xml
You can set the SSL port here too, like this.
<!-- SSL/TLS Connector configuration using the admin devl guide keystore --
port="8643" address="${jboss.bind.address}"
scheme="https" secure="true" clientAuth="false"
keystoreFile="${jboss.server.home.dir}/conf/somekeyfile"
keystorePass="changeit"
truststoreFile="${jboss.server.home.dir}/conf/somekeyfile"
truststorePass="changeit"
sslProtocol = "TLS" />
As an aside, I am using a port set that is supposed to add 200 to all my puts. This did not work for the SSL port, so I set it to the normal port + 200 as above, is server.xml.
Note that "truststore" properties are specified above, and some documentation indicates that this works. It does not. The keystore specification works however. The server will use the "tomacat" aliased certificate in the given file as it's own. I don't believe setting "truststoreFile" in server.xml has any impact.
For the truststore, clients will actually use the JRE's system trust store file. If nothing else is done but the above, to continue this example, then when this server attempts to access https://192.168.0.8:8643/something/ an exception will be thrown.
sun.security.validator.ValidatorException: PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target
This happens because the server certificate, the "tomcat" certificate provided by the server on the initial handshake, can't be found in the JRE truststore file. I added it to the somekeyfile above, but this file it not being checked. Options...
1. Add the certificate to the Jave truststore file, with the proper alias.
keytool -import -alias iws03qa5 -file tomcat.crt -keystore /opt/jdk1.6.0_30/jre/lib/security/cacerts -storepass changeit
2. Use properties set at the Java command line to specify a truststore location.
-Djavax.net.ssl.trustStore=[path and filename]
-Djavax.net.ssl.trustStorePassword=changeit
3. Set the truststore in jBoss's SSL support properties. To do this, edit:
[server directory]server/default/conf/bootstrap/security.xml
Add this, at the bottom, inside the "deployment" block:
Change [path] to your server path of course.
Interestingly, keystore properties must be given here also, even though they also appear in the other file. Otherwise, the security system will not initialize and it's a big mess.
With this setup, and the server bounced of course, the certificate is found and HTTPS works.
Friday, August 03, 2012
Trouble
I've been having a good deal of trouble with Ubuntu 1, on 11.something. Ubuntu One solidly occupies that perfect space where it is just barely stable enough to be useful, but not enough to be reliable. It is a space of peak frustration.
First, performance was terrible on my PC. I found the Ubuntu One daemon using 100% of the CPU. With a bit of Googling I found that this is a common problem - it just goes crazy for no reason. Ok... In attempting various suggested solutions, I found right off that the normal shutdown command for the sync daemon would not work. But this did:
sudo killall -9 ubuntuone-syncdaemon
I also did this:
u1sdtool -q rm -rf ~/.local/share/ubuntuone
u1sdtool -c
Also, at some point in there I did what, I guess, re-sets the local Ubuntu One "marks on the wall".
rm -rf ~/.local/share/ubuntuone
First, performance was terrible on my PC. I found the Ubuntu One daemon using 100% of the CPU. With a bit of Googling I found that this is a common problem - it just goes crazy for no reason. Ok... In attempting various suggested solutions, I found right off that the normal shutdown command for the sync daemon would not work. But this did:
sudo killall -9 ubuntuone-syncdaemon
I also did this:
u1sdtool -q rm -rf ~/.local/
and rebooted. Didn't help... An I/O nice on the process would seem to be in order:
ionice -c 3 -p $( ps h -o pid -C ubuntuone-syncdaemon )
And this seemed to help, for a few minutes I thought it was ok. But then the whole process died.
To take a step back, I think what started the trouble was that I accidentally unpacked a very large tar/zip into the sync'ed directory. The system hit my account limit. I'm here to tell you, don't let this happen. It does NOT handle it well. The software will begin to fail to connect to the service.
So while in the midst of trying to get the daemon to connect and run, I was also discovering, and deleting, the extra files. I went and deleted them from another sync'ed computer too, which I think helped.
Also, at some point in there I did what, I guess, re-sets the local Ubuntu One "marks on the wall".
rm -rf ~/.local/share/ubuntuone
But somewhere in the middle of all this I was distracted by nautilius no longer functioning. It was extremely sluggish, and eventually terminating. Again, Googling this called for deleting various files and directories - none of which worked for me.
At some point though, after deleting a lot of things, and several changes and reboots, nautilius, out of the blue started working. I unfortunately can't pin this on any specific action on my part. It just started working, while I was sitting there contemplating just going on with life, without it.
Then two things happened at about the same time. One was that Ubuntu One appeared to start working, even though CPU was still swamped.
Also, I looked at my Droid 2. Verizon's service had set the date/time on my phone to about 2 days and an hour into the future. I know it had been correct earlier in the day. One problem at a time though... Or two... Or three...
Several hours later after a lot of goofing around, nautilius and Ubuntu One are working. The date/time magically fixed itself in Verizon's network too.
However...
One of my most important files in the Ubuntu One sync directory is gone. Fortunately I have other copies, having had prior experience with Ubuntu One over-writing newer files with older files (yes, it absolutely does that, although it hasn't happen in awhile), so I can in theory, put the file back.
But when I do this, Ubuntu One instantly deletes the file and creates a new conflict file with the desired content. There appears to be nothing I can do about this. I have to call the file something else.
I really shouldn't try using software that hasn't been out for 5 years. Or should that be 10... Performance on my PC is back to normal though.
In other interesting trivia, I also had Ubuntu One running on a Windows XP machine. This was not easy to install, but that's another story. The funny thing currently is that for the past 2 or 3 weeks, if I start the Ubuntu One GUI program on that machine, a dialog appears. It tells me that an update is available and asks if I want to upgrade.
At first I clicked "yes". But nothing further happens and it has never done anything, apparently, because the dialog continues to appear. So now I don't bother.
In other interesting trivia, I also had Ubuntu One running on a Windows XP machine. This was not easy to install, but that's another story. The funny thing currently is that for the past 2 or 3 weeks, if I start the Ubuntu One GUI program on that machine, a dialog appears. It tells me that an update is available and asks if I want to upgrade.
At first I clicked "yes". But nothing further happens and it has never done anything, apparently, because the dialog continues to appear. So now I don't bother.
Tuesday, July 31, 2012
What's My IP Address?
Would you like to know your IP address for a script? There are quite a few websites that will display your IP address, but when writing script for any sort of automation, you don't want to do a lot of screen-scraping.
Try this one:
http://automation.whatismyip.
To grab the address in a bash script, use curl. Something like this will do...
IP=`/usr/bin/curl -s http://automation.whatismyip.
Try this one:
http://automation.whatismyip.
To grab the address in a bash script, use curl. Something like this will do...
IP=`/usr/bin/curl -s http://automation.whatismyip.
Wednesday, June 27, 2012
Crow Attacks!
A crow has been defending a nest for weeks by diving down on unsuspecting pedestrians and bikers on a busy sidewalk in downtown Portland.
http://www.katu.com/news/local/Bird-of-terror-This-storys-something-to-crow-about-160480945.html?tab=video&c=y
"From morning to night the bird swoops down from the sky, flying inches from the heads of unsuspecting bicyclists and pedestrians. Frequent travelers have taken to protecting themselves with umbrellas and hoods while keeping their eyes to the sky as they dash to the other side."
http://www.katu.com/news/local/Bird-of-terror-This-storys-something-to-crow-about-160480945.html?tab=video&c=y
"From morning to night the bird swoops down from the sky, flying inches from the heads of unsuspecting bicyclists and pedestrians. Frequent travelers have taken to protecting themselves with umbrellas and hoods while keeping their eyes to the sky as they dash to the other side."
Thursday, May 31, 2012
len length
Microsoft SQL Server has a function called len() while MySQL has a function called length().
There doesn't seem to be any common way to write SQL that will work in both servers. So I guess my Java program will have to resort to detecting the server type from a JDBC Connection and making the necessarily adjustments to the queries.
Connection con;
DatabaseMetaData databaseMetaData;
...
databaseMetaData = con.getMetaData();
if (databaseMetaData.getDatabaseProductName().contains("Microsoft"))
{
/*
* SQL Server, boo!
*/
}
else
{
/*
* MySQL, hotdog!
*/
}
For what it's worth SQL Server appears to be the out-of-spec one of the two (shocking I know).
There doesn't seem to be any common way to write SQL that will work in both servers. So I guess my Java program will have to resort to detecting the server type from a JDBC Connection and making the necessarily adjustments to the queries.
Connection con;
DatabaseMetaData databaseMetaData;
...
databaseMetaData = con.getMetaData();
if (databaseMetaData.getDatabaseProductName().contains("Microsoft"))
{
/*
* SQL Server, boo!
*/
}
else
{
/*
* MySQL, hotdog!
*/
}
For what it's worth SQL Server appears to be the out-of-spec one of the two (shocking I know).
Thursday, May 17, 2012
Fat Cat
This is Iris the cat.
I took this cat, Iris, to the vet for a checkup first thing this morning.
Strictly routine...
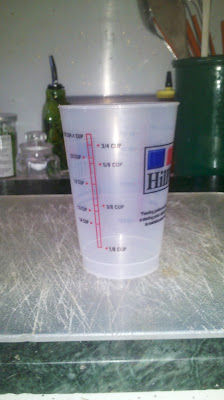
The vet said she was too fat and gave me this cup to measure the cat food.
I have two cats, the other one being thin and smaller generally, so there's some guess work involved, but she suggested about how much food they should both eat in a day.
I took the food I had just given them this morning, hardly any eaten yet due to the trip to the vet, and poured into the measuring cup. Here's the problem.
It's almost exactly what it is supposed to be.
The vet said she was too fat and gave me this cup to measure the cat food.
I have two cats, the other one being thin and smaller generally, so there's some guess work involved, but she suggested about how much food they should both eat in a day.
I took the food I had just given them this morning, hardly any eaten yet due to the trip to the vet, and poured into the measuring cup. Here's the problem.
Wednesday, February 01, 2012
Bring Back the Incoming Stream
Google+,
Having the Incoming steam, I can share with Extended Circles. Persons I don’t know, but have a real connection to, through another person, may see those items. They are free to ignore them, or add me to a circle themselves. They can even easily ignore the Incoming stream altogether if they like. Without the Incoming stream, it’s first of all hard to see the point of the Extended Circles option at all. But even more importantly, I have no incentive to grow my own circles, beyond what I actively read, to included interested persons.
This devalues the whole idea of Circles by removing one of their innovative applications. Circles are used both to read incoming items, and to direct out-going content. Without the Incoming stream, there’s no functional middle ground in out-going items between a carefully directed shared item, limited to people I know fairly well, and a completely public item.
The idea that the suggested friends display in circle management is a suitable replacement is almost laughable. Items appearing in my Incoming stream are items expressly made available by someone I don’t (yet) know, to me. The suggested friend list is nothing more than an selection of Google executives, billionaires, pop stars and assorted internet celebrities.
Google+, do you want our circles to be a core collection of 100 or so people we directly interact with, plus William Shatner, Robert Scoble, Larry Page and a few others so widely followed that they don’t even know we exist? Or do you want us to crowd source vast networks of people with common interests in labeled collections?
Google+, please bring back the Incoming stream.
Thank you.
Subscribe to:
Posts (Atom)
Jeff Sexton
007
1:144 Scale
1:350 Enterprise
10 Barrel Brewing
14
1856
2001 A Space Odyssey
3D modeling
40and20
4th of July
78 RPM
Abyss
Adam West
Advertising
Agora Models
Air Canada
Airline
Airways Brewing
Alan Bennett
Alaska
Alberta
Alberta Street Pub
Alfa Romeo Spider Touring Gran Sport
Amati
Amazon
Amnesia Brewing
AMT
Analog signal
Android
Anomalies and Alternative Science
Antiques
Apache
Apollo
Apple
Apple Stores
Art
Artisanal Beer Works
Assembly Brewing
Aston Martin
Astoria
Asus
Atlas
Audrey
Augmented reality
Aurora Famous Fighters
auto-awesome
Automobile
Autos
Aviary
Aviation
Backups
Baelic Brewing
Bale Breaker Brewing
Bandai
Barack Obama
Barley Brown's Beer
Bars
Base Camp Brewing
Batman
Battery
Beards
Beer
Beer Bar
Bell System
Bellwether
Berkshire Hathaway
Betty White
Beyond the Fringe
Bigfoot
Bikes
Bill Clinton
Bird Food
Bird Toys
Birds
Birthdays
Bleriot
Bleriot XI
Block 15 Brewing
Blogger
Bojack Horseman
Bolton Landing Brewing
Boltons
Boneyard Brewing
Books
Boxer Ramen
Boxer Ramon
Breakside Brewing
Brian Eno
Build Management
Buoy Brewing
Burger King
Business and Economy
Business Process Execution Language
Bye & Bye
Byte-order mark
Canadian
Carrot
Cats
Chex Mix
Chihuly
Chipmonk
Christmas
Civil Defense
Clinton
Clocks
Closet Doors
CNN
Cockatiels
Cocktails
Collections
Columbia Grafonola
Columbia River George
Columbia River Gorge
Corners
Corvallis
County Cork
Crooked Stave Brewing
Crows
Crux Brewing
Cuisinart
Culmination Brewing
David Byne
DB5
Dear Jane
Debian
Deschutes Brewing
DFW C.V
Diabetes
Dick Curtis
Digital Living Network Alliance
Digital television
Dinosaurs
Disney
Doll House
Don the Beachcomber
Double Mountain Brewing
Dow Jones Industrial Average
Dragons
Dudley Moore
Duesenburg SJ Roadster
Durham University
DVD
E-mail address
E9
Eagle
Eagle Creek Fire
Eaglemoss
Easter
ebauche
Ecliptic
Economics
Ed
Ed and Olive
Eels
EJB
Elgin
Elysian Brewing
Energy development
Enterprise
Enterprise JavaBean
ESP
Evergreen Air Museum
Everybody's Brewing
Ex Novo Brewing
F-84G Thunderjet
Facebook
Family Photos
Fathers Day
Fearless Brewing
Fedora
Ferment Brewing
Ferns
Festival of The Dark Arts
Filesharing
Finance
Finger
Firesign Theater
Fireworks
Flowers
Flying Sub
Food
Ford
Fort George Brewing
Fossil fuel
Free House
Garfield James Abram
Garfield Minus Garfield
Gateway Brewing
Gene Sexton
Gene Wilder
George Carlin
Gigantic Brewing
Gilgamesh Brewing
Glass
Glassfish
Global warming
Golden Arches
Goldfinger
Goofy
Google
Google Assistant
Google Buzz
Google Docs
Google Home
Google Lively
Google Photos
Google Reader
Google Wave
Google+
Goose
Graffiti
Grammar
Gravy
Great Divide Brewing
Great Notion Brewing
Greek Festival
Greenhouse gas
Gruen
GT40
H. G. Wells
Half-Life 2
Halloween
Harlan
Hawaii
Helbros
High-definition television
Hilo
Hilo Brewing
History
Ho 229
Hollywood Theater
Hopworks Urban Brewery
Horizon Models
HP
Hybrid electric vehicle
IBM
Impala
Inner city
Instagram
Insulin
Investing
IPMS
Iris
Irony
J.C. Penny
James Bond
Jane Austen
Java
Java Architecture for XML Binding
JC Penny
JDBC
Jeannine Stahltaube
Jeff's!
Jim Davis
joe the plumber
John McCain
Jonathan Miller
Jubelale
Kapaau
Karma
Kauai
Kay Thompson
Kermit the Frog
Keys
Keys Lounge
Kids and Teens
Kona
LA Auto Show
Labrewtory
Larry King
Laser
Laserdisc
Leavenworth Wenatchee River
Level Brewing
Lilly Tomlin
linux
Little Beast Brewing
Lloyd Center
Logging
Lowry Sexton
LPs
Lucky Lab
Magnets
Mark Cuban
Market trends
Martin Mull
Maytag
McDonald
Mediatomb
Meier and Frank
Mel Brooks
Mercury
Microsoft
Microsoft Windows
Migration Brewing
Mobius
Models
modern Times Brewing
Money
Monkey
monsters
Moon
MOUNT HOOD
Mount Tabor
Movie Reviews
Multnomah Falls
Music
Music industry
Muxtape
MySQL
NetBeans
Netflix
Nikon
Nikon Z50
Ninkasi Brewing
Nintendo
Nissan Cube
Norm Coleman
North Bar
Nuclear fallout
Nuclear warfare
Nuggest
Nuts
OBF
Office Depot
Offshoot Beer Co
Oktoberfest
Ola Brewing
Old Town Brewing
Olive
Open ESB
Oracle Corporation
Orca
Oregon
Orion Space Clipper
Owls
Pacific Ocean
Packard Boattail
Pam American
Parrots
Patio Sale
PDX
Pearl District
Pearl District Portland Oregon
Peppers
Performance Review
Peter Cook
Peter Iredale
Pets
Pfriem Brewing
Philip K Dick
Phone Book
photography
Pizza
Plank Town Brewing
Play Station
PlayStation 3
pluspora
Pocher
Podcast
Poke
Pokémon HeartGold and SoulSilver
Polar Lights
Politics
Pono Brewing
Portal
Portland
Portland Development Commission
Presidents
Pride and Prejudice
Programming
Projects
PS3
PS4
Pumpkins
Quotation Marks
Rad Power
Radio
Radio Room
Ramen
Ramon
Recipes
Recording Industry Association of America
Renewable energy
Reservoir
Reuben's Brewing
Reubens Brewing
RIAA
Richmond Pub
Robot Chicken
Rock-paper-scissors
Rogue Brewing
Round 2
Sales
San Francisco
Santa
Sarcasm
Sasquatch Brewing
SATA
Science fiction film
Sea Quake Brewing
Seattle
Selfie
Serbia
Service-oriented architecture
Seward
Shelby Cobra
Shipwreck
Shopping
Signs
Silver Moon Brewing
Slide Rule
Snow
Soap
Soap Cutter
Social Security
Social Studies
Society6
Sony
Sopwith F.1 Camel BR.1
Soviet
Space 1999
Space Race
Spad XIII
Speaker Repair
Spirit of St. Louis
Spitfire
SQL
Squirrel's
St Patricks Day
Stanford Hospital
Star Trek
Star Wars
Starbucks
Stock market
Storm Breaker
Strip search
Stripes
Studebaker
Studellac
Sun Microsystems
Supernatural
T-Mobile
Tablet
Tamiya
Tamiya Spitfire
Taube
TechCrunch
Technical
Television
Terminal Gravity
Thanksgiving
The Producers
ThinkGeek
Three Creeks Brewing
Thunder Island Brewing
Tiki
Time Bandits
Toaster
Tom Peterson
Tools
Top Ferment
Total Recall
Transportation Security Administration
Trumpeter
Tubboat
Tyco
UFOs
Unicode
United States
United States Department of Homeland Security
Universal Plug and Play
Unknown Primates
USB
USS Yorktown
Valcom
Van Gilder Hotel
Vegetable garden
VHS
Victoria
Video
Video game
Vintage Images
Vintage Vintage!
Virtual world
Volcano Hawaii
Volvo C70
Voyage to the Bottom of the Sea
Wall Street
War of the Worlds
Warren Buffett
Warrenton
watches
Watercolor
Wayfinder Brewing
We Can Remember It for You Wholesale
Web service
Web Services Description Language
Whiskey
Wii
Windows 7
Windows Phone 7
Windows Vista
Windows XP
Windy
Wingnut Wings
Wood
Worthy Brewing
WWI
WWII
X-Files
X-ray vision
XML
XML Schema
Y2K
Yeti
YouTube
Yugo
Zero Mostel
Zima
Zoom H2n